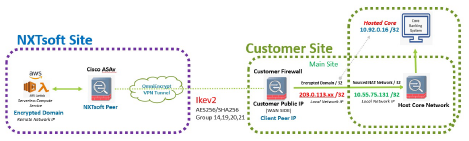
OmniEncrypt establishes a secure connection from each client site to our AWS environment. This connection is secured using strong encryption and authentication methods. OmniEncrypt uses a load balance appliance at the site to securely route traffic to the core system.We provide 24/7 monitoring of this solution. Also, there is an additional option for automatic WAN failover to a cellular uplink, this option will allow connectivity to continue when the client’s internet is down.
NXTsoft
- ASAv inside of AWS environment
- Serverless Compute (Lambda)
- Encrypted Domain (172.31.240/24) (The range of IP address of the host which will be participating in the encrypted IPSEC/VPN Tunnel)
- Preferred: non-RFC1918 IP Range, due to overlapping with other customers
- IKEV2 is recommended
- Encryption AES-256
- Hashing method SHA256
- Diffie-Hellman (DH) group 14,19, 20, 0r 21
- No PFS
- Phase-1 (ISAKAMP) lifetime 86400
- Phase-2 (IPsec) lifetime 28800
Client
- Peer IP for Main Site
- /32 or Encrypted Domain
- /32 for Source Nat
- Flexibility to use your own policy on allowed ports open to core
- Support for Policy Base IPSEC VPN
- Support for VTI (Route Based)
- Configure info from above exhibit
- 203.0.119.xx/32 is mapped to the Vendor Core IP address
- 10.55.75.131 is the source NAT traffic to the Vendors Core
- -203.0.119.xx/32 would be the encrypted domain for the IPSEC VPN tunnel
- -10.55.75.131 would be the source NAT
- -203.0.119.xx is RFC-5737, You can use your own IP if non-overlapping with NXTsoft Clients
Let our data experts evaluate your organization’s needs with a free discovery call.
We love tailor-fitting solutions for any size company.


